We can say this about a lot of things but in particular with respect to “proving that somebody hacked into something” it is extremely unlikely that it can be ‘elevator pitched’ so that the average citizen can understand. But for Trump to hand-wave away the work of our country’s intelligence specialists and suggest “meh, hard to say for sure” is just so… burns me up.
I’m not sure about that. Read this tweet thread - it’s pretty clear what’s up:
Can you summarize? I’m kind of shit at reading tweet chains and infosec gobbledygook.
To show a video of how ‘the russians hack things’ they could just show a video of a typical employee opening an email with an attachment, with instructions in poor english informing the user that they need to activate Macros (despite being warned against it by the application) to “view the document”.
Pretty advanced stuff.
The people that sent Podesta the phishing link that stole his gmail credentials used bit.ly in order to shorten the urls to the pages to steal the credentials. The account they made at bit.ly in order to generate these shortened links was used to generate a different link for each email, and they used it to send a lot of emails. If you look at the emails that were being targeted, they have clear trends. Scroll down on this page for the pie charts for what those emails were involved in:
Actually I can quote it here:
Target analysis
CTU researchers analyzed the Google Accounts targeted by TG-4127 to gain insight about the targets and the threat group’s intent.
Focus on Russia and former Soviet states
Most of the targeted accounts are linked to intelligence gathering or information control within Russia or former Soviet states. The majority of the activity appears to focus on Russia’s military involvement in eastern Ukraine; for example, the email address targeted by the most phishing attempts (nine) was linked to a spokesperson for the Ukrainian prime minister. Other targets included individuals in political, military, and diplomatic positions in former Soviet states, as well as journalists, human rights organizations, and regional advocacy groups in Russia.
Other targets worldwide
Analysis of targeted individuals outside of Russia and the former Soviet states revealed that they work in a wide range of industry verticals (see Figure 6). The groups can be divided into two broad categories:
Authors, journalists, NGOs, and political activists (36%)
Government personnel, military personnel, government supply chain, and aerospace researchers (64%)
TG-4127 likely targeted the groups in the first category because they criticized Russia. The groups in the second category may have information useful to the Russian government.
https://pbs.twimg.com/media/C1U-Ga4XgAAmMzY.jpg
Figure 6. TG-4127 targeting outside of Russia and former Soviet states. (Source: SecureWorks)
Authors and journalists
More than half (53%) of the targeted authors and journalists are Russia or Ukraine subject matter experts (see Figure 7). It is likely that the Russian state has an interest in how it is portrayed in the media. U.S.-based military spouses who wrote online content about the military and military families were also targeted. The threat actors may have been attempting to learn about broader military issues in the U.S., or gain operational insight into the military activity of the target’s spouse.
https://pbs.twimg.com/media/C1U-YcTW8AE7yvv.jpg
Figure 7. Subject matter expertise of authors and journalists targeted by TG-4127. (Source: SecureWorks)
Government supply chain
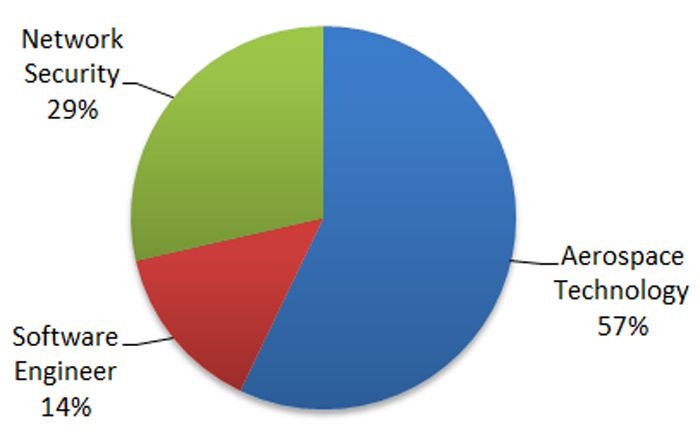
CTU researchers identified individuals who were likely targeted due to their position within the supply chain of organizations of interest to TG-4127 (e.g., defense and government networks). Figure 8 shows the distribution by category. The targets included a systems engineer working on a military simulation tool, a consultant specializing in unmanned aerial systems, an IT security consultant working for NATO, and a director of federal sales for the security arm of a multinational technology company. The threat actors likely aimed to exploit the individuals’ access to and knowledge of government clients’ information.
Figure 8. Categories of supply chain targets. (Source: SecureWorks)
Government / military personnel
TG-4127 likely targeted current and former military and government personnel for potential operational insight gained from access to their personal communications. Most of the activity focused on individuals based in the U.S. or working in NATO-linked roles (see Figure 9).
https://pbs.twimg.com/media/C1U-yQQWEAEQglQ.jpg
Figure 9. Nation or organization of government/military targets. (Source: SecureWorks)
TG-4127 targeted high-profile Syrian rebel leaders, including a leader of the Syrian National Coalition. Russian forces have supported Syrian President Bashar al-Assad’s regime since September 2015, so it is likely the threat actors are seeking to gain intelligence on rebel forces to assist Russian and Assad regime military operations.
Edit: finished formatting as much as I’m going to
I totally trust the guy that can’t use a computer and thinks we should have couriers over the intelligence services of a super power.
I also trust my medical treatment to the guy at the gas station because he can sell me aspirin.
Couriers are so old fashion. I say we institute the tube system again. Every office gets a tube, and you shove your piece of paper in this little plastic capsule and watch it race through the bowels of old buildings. When rats get into those tubes, we get all our representatives cats. Everyone will be a lot happier with cats around anyways. It might be a problem when we start sending pigeons out to our foreign diplomats but the pigeons meeting the cats will just provide entertainment. Based on our voting block, all they care about is entertainment anyways.
Waiting for the Trump tweet complaining that the declassified report wasn’t released today as promised (would be even more awesome if he replied to the above tweet).
It’s hard to believe our President is publicly feuding with the entirety of US intelligence while tweeting about how smart Putin is and whatever. Like HOLY CRAP.
May you live in interesting times and all that.
Why this could be? I am a naive person and I know very littel of politics. Sounds to me like Trump wants to gut these agencies and force them to obey the executive and not get out of the “narrative” announcing things that make the politicians in power feel uncomfortable. A scare tactic.
I dunno. But computers are designed to share information. So maybe If you have a secret that you really dont want anyone else to read, don’t put in a computer? sound good to me. But using couriers… that have his own problems, like the courier losing the package.
Yeah, you wouldn’t want your intelligence services to be able to like… share information or anything.
Better to send everything by hand so you’re always a week behind the other guy. Assuming said info ever gets anywhere.
I am happy that I don’t have to take these decisions.
If you are going to do something nasty and store in a computer information about it, somebody may find this information and share it with everyone.
The best way to stop a leak is to not store the secret anywhere.
Websites do this for passwords. A website like quartertothree.com don’t really store our password, store a hash of our password, so if somebody manage to break the security of the server and download the database, they will not have the passwords of 1000+ people, they will have a bunch of hash.
The computer is amazing at editing information, sharing it… is not so great has a fortress that protect it from enemy eyes.
So we just print out the petabytes of sigint we intercept daily and put the stacks of paper in Yucca Mountain?
We can deforest the Amazon in order to get the paper.
And we can use detained Muslims and Mexicans as labour to retrieve the data as we need it!
This will also punish Jeff Bezos, who I hear is a huge loser!